Key Takeaways:
- Quantum computing threat to crypto centers on breaking digital signature algorithms that protect wallet ownership
- Approximately $440 billion in Bitcoin sits in vulnerable legacy addresses that quantum computers could attack
- Bitcoin’s BIP 360 proposal marks the first formal step toward quantum-resistant address formats
- Experts estimate quantum computers capable of breaking crypto encryption could arrive between 2030 and 2040
The quantum computing threat to crypto became more concrete in February 2026 when Bitcoin developers published BIP 360, formally addressing one of the blockchain’s most significant long-term security challenges. A sufficiently powerful quantum computer could theoretically derive private keys from public keys, breaking the elliptic curve cryptography that secures Bitcoin, Ethereum, and most major cryptocurrencies. This would allow attackers to forge signatures and drain wallets, fundamentally undermining the security model that makes cryptocurrency trading possible.
What Makes Quantum Computing Dangerous for Crypto?
The quantum computing threat to crypto operates through two main attack vectors, each targeting different aspects of blockchain security. Shor’s algorithm represents the existential threat because it allows quantum computers to reverse-engineer private keys from exposed public keys. This directly attacks the digital signature schemes that prove ownership and authorize transactions across all major blockchains.
Current cryptography relies on mathematical problems that classical computers find practically impossible to solve. Factoring large prime numbers or solving discrete logarithm problems would take conventional computers thousands of years. Quantum computers using Shor’s algorithm could potentially solve these same problems in hours or minutes once they reach sufficient scale and stability.
Grover’s algorithm poses a secondary but manageable threat to hashing functions like SHA-256 used in Bitcoin mining and address generation. This algorithm provides a quadratic speedup, effectively halving security levels from 256-bit to 128-bit strength. Developers consider this addressable through increased hash sizes or adjusted mining difficulty without fundamental protocol changes.
The Timeline Question
Research estimates for when quantum computers could break current crypto encryption vary significantly. Most experts place “Q-Day” somewhere between 2030 and 2040, with some studies suggesting a 17% to 34% probability of a breakthrough by 2034. Breaking Bitcoin specifically would require an estimated 13 million to 1.9 billion stable logical qubits depending on the efficiency of error correction methods.
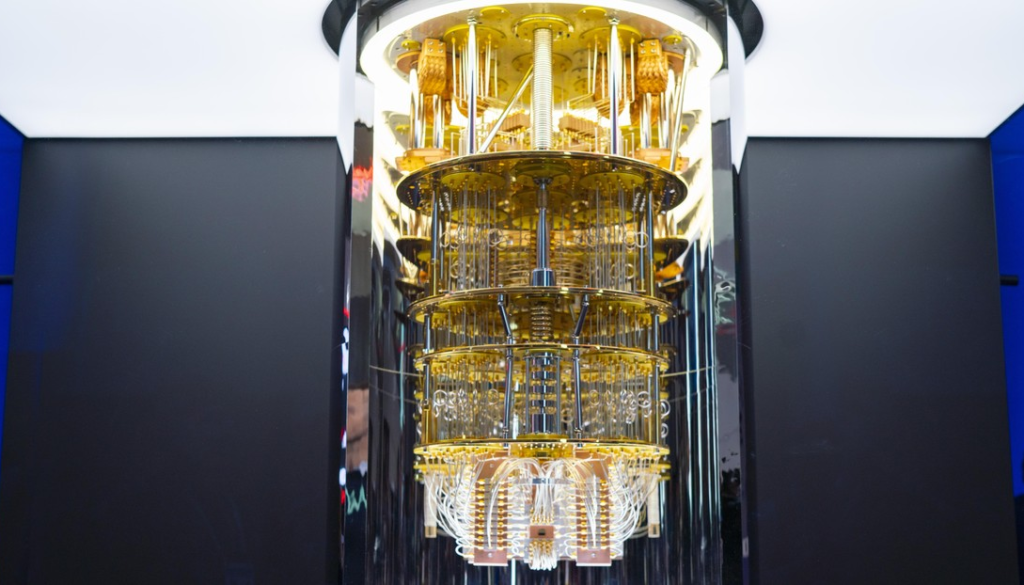
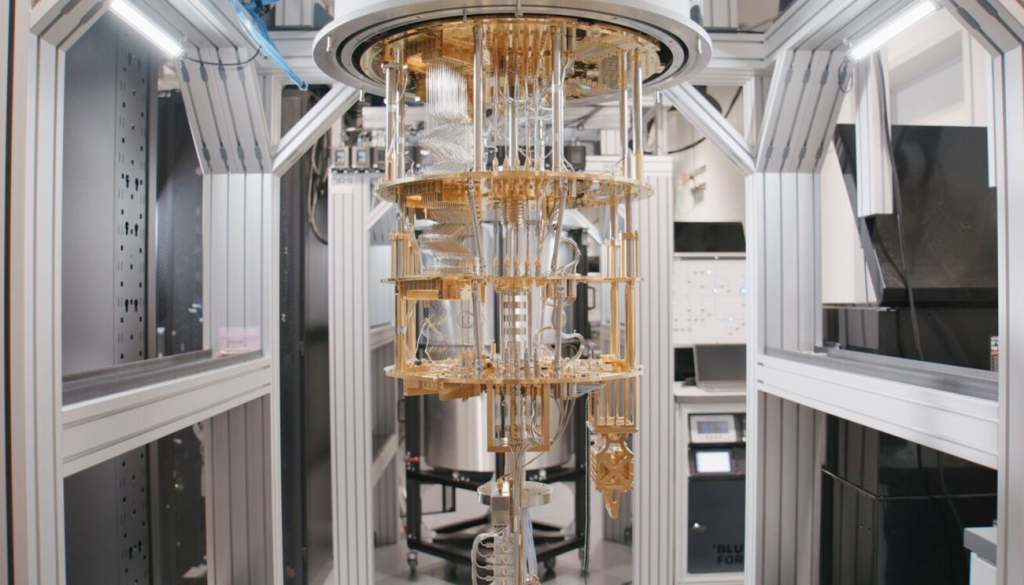
Google’s Willow processor, released in late 2025, demonstrates where current quantum hardware stands. The chip contains just 105 qubits, showing the massive gap between today’s capabilities and the scale needed to threaten blockchain cryptography. However, the required qubit count keeps falling as researchers develop more efficient algorithms and better error correction techniques.
How Much Crypto Is Currently Vulnerable?
The quantum computing threat to crypto affects different holdings unequally based on address formats and usage patterns. A Human Rights Foundation report from October 2025 quantified Bitcoin’s exposure using data from the Presidio Bitcoin Quantum Summit. Approximately 1.72 million Bitcoin worth over $115 billion sits in very early address formats considered highly vulnerable to long-range quantum attacks.
An additional 4.49 million Bitcoin valued at approximately $300 billion faces vulnerability to long-range attacks, though owners could protect these holdings by migrating to quantum-secure address types once available. Combined, this represents over $415 billion or roughly 31% of Bitcoin’s circulating supply by value.
Legacy P2PK addresses where public keys are permanently exposed on the blockchain face the highest risk. These addresses include many coins from Bitcoin’s earliest years, some potentially belonging to creator Satoshi Nakamoto. Modern address formats like Taproot P2TR offer better protection but still contain quantum vulnerabilities that BIP 360 aims to eliminate.
The “harvest now, decrypt later” attack vector adds urgency to this timeline. Sophisticated adversaries are currently collecting blockchain transaction data to store until quantum computers become powerful enough to crack the encryption. This means coins that seem secure today could become vulnerable the moment quantum capabilities cross a threshold.
What Is Bitcoin Doing About This Threat?
Bitcoin developer Murch announced BIP 360 on February 11, 2026, marking the cryptocurrency’s first formal step toward quantum resistance. The Pay-to-Merkle-Root proposal, authored by Hunter Beast, Ethan Heilman, and Isabel Foxen Duke, introduces a new output type that builds on Taproot’s architecture while eliminating its primary quantum vulnerability.
Current Taproot addresses expose public keys during keypath spends, creating the opening quantum computers could exploit. BIP 360’s P2MR addresses commit to a Merkle root of a Tapscript tree instead, keeping public keys hidden until transactions are spent. Even then, exposure is minimized compared to existing formats.
The proposal represents step one in a multi-phase process toward full quantum resistance. Co-author Ethan Heilman explained to CoinTelegraph Magazine that adopting post-quantum signature algorithms will be required as step two. BIP 360 establishes quantum-resistant outputs with Taproot’s upgradability and features but without the quantum vulnerability.
What BIP 360 Doesn’t Solve Yet
The proposal addresses long-exposure attacks where quantum computers analyze public keys permanently visible on the blockchain. It doesn’t solve short-exposure attacks where quantum computers could derive private keys during the seconds or minutes transactions sit in the mempool before confirmation. That requires different post-quantum signature algorithms the development team plans to introduce later.
Post-quantum signatures create practical challenges because they’re significantly larger than current ECDSA signatures, potentially ten times the size. Without accompanying changes to block size or compression methods, a fully quantum-resistant Bitcoin could process far fewer transactions per block than today’s network handles.
How Are Other Blockchains Responding?
The quantum computing threat to crypto has prompted different response strategies across major networks. Ethereum formed a dedicated post-quantum working group with community support for a full protocol overhaul by 2029. Vitalik Buterin unveiled a roadmap in February 2026 including EIP-8141 to transition Ethereum toward quantum-resistant hash-based signatures and STARK proofs.
Solana experimented with post-quantum signatures and moved its Alpenglow consensus upgrade from concept to testnet in under a year. The faster development cycle reflects Solana’s more centralized governance structure compared to Bitcoin’s consensus-driven approach.
Some projects built quantum resistance into their foundation from the start. Quantum Resistant Ledger uses NIST-approved XMSS signatures, while Starknet gains inherent protection through STARKs that rely on quantum-safe hash functions. QANplatform employs lattice-based cryptography specifically designed for enterprise-grade security against quantum attacks.
The NIST Standards Framework
The National Institute of Standards and Technology finalized the first post-quantum cryptography standards in August 2024. ML-KEM based on Kyber and ML-DSA based on Dilithium now serve as benchmarks for blockchain upgrades. These standards give developers concrete targets for implementing quantum-resistant cryptography rather than experimental approaches.
The US federal government mandated a phase-out of ECDSA cryptography by 2035, while the NSA’s CNSA 2.0 framework requires quantum-safe systems across critical infrastructure by 2030. The Department of Defense set an internal deadline of December 31, 2030, for quantum-ready systems. These timelines suggest governments view the quantum computing threat to crypto as requiring action within this decade.
What Should Crypto Holders Do Right Now?
BIP 360 changes nothing for holders today because it’s a proposal awaiting review, debate, and eventual implementation. The practical timeline for Bitcoin achieving full quantum resistance spans approximately seven years assuming immediate agreement. Three years for finalizing BIPs, completing code review and testing, and reaching community consensus. Six months for activation. Then additional years for wallets, custodians, exchanges, Lightning Network nodes, and treasury software to upgrade.
Holders using modern Taproot P2TR addresses should monitor developments and prepare to migrate to quantum-resistant address types once they become available on mainstream wallets. Most current hardware and software wallets avoid address reuse and don’t use vulnerable P2PK formats, meaning the majority of retail holders aren’t in the highest-risk categories today.
Institutional holders and custodians face more urgent timelines because custody infrastructure takes years to upgrade. The DoD’s 2030 deadline and the government’s 2035 ECDSA phase-out should inform how treasury and custody teams approach their migration roadmaps now rather than waiting for quantum computers to arrive.
The “burn or steal” dilemma remains philosophically charged. If quantum computers arrive before dormant early-format addresses migrate, should Bitcoin freeze those coins to prevent theft or allow attackers to plunder them? That question touches Bitcoin’s core principle of holding immutability and remains unresolved within the developer community.
Frequently Asked Questions
When will quantum computers actually break crypto?
Most experts estimate quantum computers capable of breaking current crypto encryption will arrive between 2030 and 2040. Some research suggests a 17% to 34% probability by 2034. Breaking Bitcoin requires an estimated 13 million to 1.9 billion stable logical qubits, far beyond current capabilities.
Which cryptocurrencies are most vulnerable?
Bitcoin holdings in legacy P2PK addresses where public keys are permanently exposed face the highest quantum computing threat to crypto. Approximately $115 billion in very early Bitcoin addresses are considered highly vulnerable. Modern address formats offer better protection but still contain vulnerabilities that upcoming proposals aim to eliminate.
Can quantum-resistant crypto be developed?
Yes, multiple approaches exist for quantum-resistant cryptocurrency. NIST finalized post-quantum cryptography standards in August 2024 including ML-KEM and ML-DSA. Projects like Quantum Resistant Ledger already use these approved algorithms. Major networks like Bitcoin and Ethereum are developing migration paths to implement quantum resistance.
What happens to Satoshi’s Bitcoin?
The roughly 1 million coins in early P2PK addresses widely attributed to Bitcoin’s creator cannot migrate to quantum-safe formats without private keys nobody is known to hold. Whether to freeze those coins or leave them vulnerable represents one of the most philosophically challenging questions in Bitcoin’s history.
Should I move my crypto to different wallets?
Holders using modern wallet software that doesn’t reuse addresses face lower immediate risk from the quantum computing threat to crypto. Moving funds to quantum-resistant address formats makes sense once those options become available on mainstream wallets, likely within the next few years as proposals like BIP 360 move toward implementation.
















